On This Page: [hide]
This article has been created with the main idea to help explain what exactly is the Web Security Gateway technology and how both companies and end-users can benefit from this technology for server safety. Here, we aim to explain to you what exactly does this type of technology work and how it can benefit exactly, plus what it is effective against.
What Is а Web Security Gateway?
Web Security Gateway is a technology that has been created to protect both organizations and end-users by using one simple method – traffic filtering and filtering of Internet traffic. Now it all may sound good and simplistic until you take a closer look at how it exactly functions.
The main “location” of this technology is primarily between the users and the internet. These types of gateways are specifically configured so that they can ensure network safety on an advanced and professional level. This is achieved by using technologies for safety, such as URL filtering, Application Control, prevention of data loss, antivirus, and HTTPS inspection of sites. The main idea behind this is to help organizations have significantly stronger online safety.
What Are the Pros and Cons of a Web Security Gateway?
Companies nowadays are competing on who will offer a WSG that has more features than its competitor when it comes to protecting your server. And the one that has the most features is not always the cheapest as well. But also, bear in mind that it is created to repel various types of threats and the main idea here is that it needs to have the primary features to do so. Below, we are going to show you more information about those features.
Pros:
Easy to implement.
Takes a short time to learn if you are an experienced administrator.
Provides security not only against malware but also other more innovative threats and threats during browsing.
Most products have automatic learning based on reporting and are constantly being updated in real-time with new threats.
Cons:
Every brand has different Gateway software that makes it difficult to accustom to because of new menus, settings and other aspects.
Some WSG are more accustomed to block specific threats than others. Choose wisely.
Adding features to your WSG could end up being very pricey.
Feature #1: WSG Can Filter Out Malware, Social Media Threats, Virus Content, Rogue Apps
Most Gateway technology systems of this type have the capability to let organizations benefit from online apps and tools without the company’s network actually being exposed to malware that is online-based. The main idea here is to cut virus infection, loss of user information, and also misusage of the network traffic. Being a solution for online security and also easier management the technologies incorporated in these gateways often incorporate the following protection:
- Malware protection.
- Spyware security.
- Adapting of new requirements.
- Threat reporting and automatic learning.
- Social-network regulating.
- Visibility of SSL-encrypted traffic.
- Remote filterings.
Feature #2: Following Strict Policies of Corporate Organizations
This Gateway technology aims to not only exist and protect but also be there to improve. Its main benefit is to increase the productivity of companies, prevent behavior that is risky, regulate the usage of bandwidth and also enforce policies on the activities of users. Most such platforms also aim to make sure they follow these criteria points:
- Groups.
- Traffic.
- Users.
- Time.
- Others set by the administrators.
Furthermore, the SSL-filtering and inspection capabilities also aim to provide enforcement on social media as well as searching platforms which are usually obfuscated.
Feature #3: Threat Protection that Is Online-Based
Another important feature of this technology is that it successfully manages to ensure threat protection on web threats. This happens by incorporating definitions and anti-malware technologies that have real-time protection and active shield against the following types of threats:
- Malicious requests by virus URLs.
- Viruses.
- Spyware.
- Advanced web filtering against scam and other risky domains.
Feature #4: Constant Tracking of Web and User Activity
Most of these Gateway technologies also aim to ensure that the user gets insight into the activity and threats that are occurring via some form of user-friendly command and control center. Such control and monitoring layout allows the admins the create a good policy strategy for security and swiftly oversee and respond to threats based on this activity.
Some companies offer platforms that combine the reports from each organization discretely in order to make the platform more responsive and boost protection and some also aim to enable to present aggregated updates for interconnected devices.
Feature #5: Easy Setup and Control
One of the best features of these types of tech is that they are mostly cloud-based and they allow easy management and quick setup and installation and administrators can be educated to operate with these technologies quickly.
Which Are The Best Web Security Gateways?
There are many technologies to choose from and they are all good. But when it comes to the best, the following five are what we believe among the best in the business:
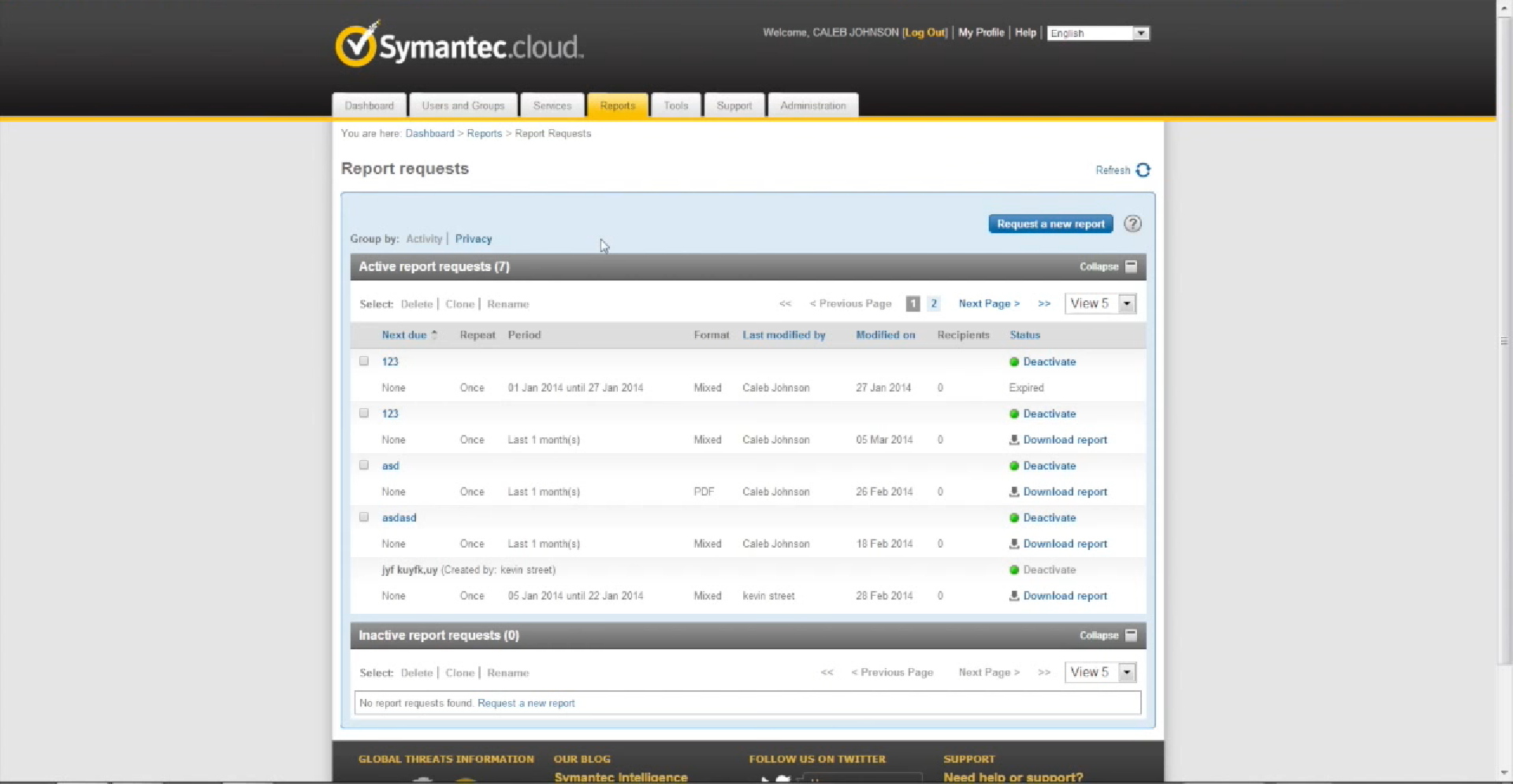
1. Symantec Secure Gateway
The cloud-based internet security gateway by Symantec is created to adequately solve the safety problems by combining data loss prevention, e-mail protection, cloud access protection broker, and advanced threat detection capabilities. They also have machine learning and image analysis and automatic threat removal.
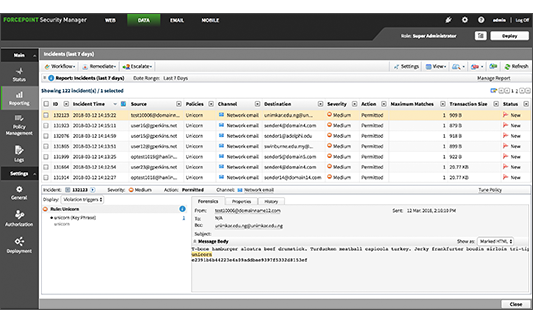
2. Forcepoint
Forcepoint Web Security is a technology which also has URL Filtering, data loss prevention, advanced malware detection, advanced classification engine, cloud sandboxing to contain viruses, and 100% accuracy when an attack is imminent. It also offers quite a good license system that allows flexibility and scalability.
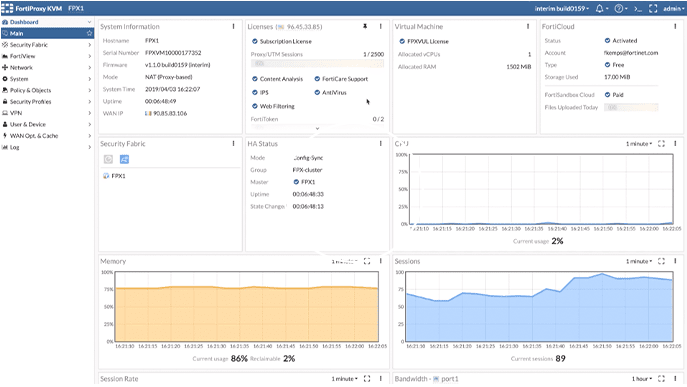
3. FortiProxy
Created by one of the largest cyber-protection companies FortiNet, FortiProxy is designed to offer both antivirus, filtering, DNS filtering, applications controls, data leak protection, content management and analysis, traffic analysis, intrusion prevention, VPN access, ICAP integration, sandboxing, and many other top-of-the-line technologies. The system is capable of inspecting SSL and SSH traffic to hidden deeply concealed threats to safety.
4. Barracuda
The tool by Barracuda for filtering is perfectly capable of protecting your organization from all types of threats. The software is able to analyze SSL traffic and filter internet content from afar. It uses threat intelligence, antivirus, and also anti-spyware which allows it to cover various online threats. Its main goal is the advanced threat protection it has which performs check for files and compares them in a cryptographic hash-based content to block any virus code.
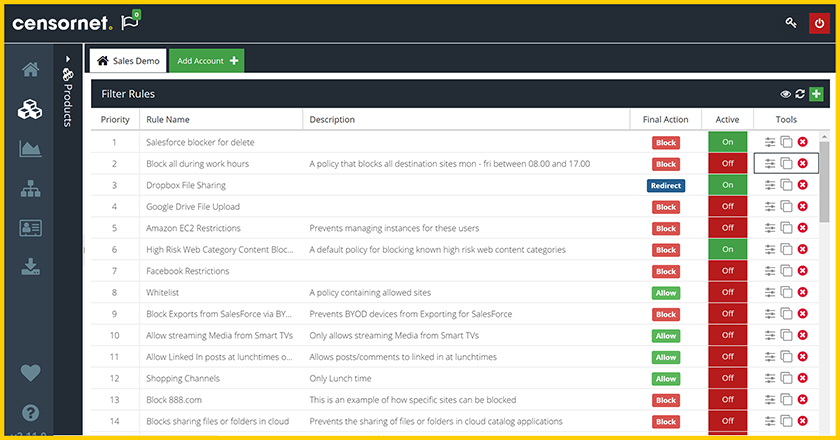
5. Censornet
Being one of the biggest websec cloud services has its perks and one of those perks is the experience you gain. Censornet has used its experience to create a great tool that can block various types of content. Such content can be malware-related, inappropriate, imagery, illegal content, offensive, extremist, adult, and others. Overall and all Censornet is the choice you would make if you are keen on censorship of such content.
Conclusion on Web Security Gateway
To protect your servers and organizations online is not a question of whether you want to anymore and setting up adequate protection is a must. In case your employees or clients are connecting to services that are cloud-based or apps, this type of protection is perfect for finding threats among this type of encrypted traffic.
More Tips by Howtohosting.guide:
Always choose a service that will suit your need.
Know your budget.
Know what specific type of content you are dealing with and want to block out.
Make sure to ask about the pricing, because it could go high as you want more features added.